BITRESURRECTOR
BitResurrector is free software designed to search for abandoned Bitcoin assets by generating private keys and instantly checking them for balances on the associated addresses.
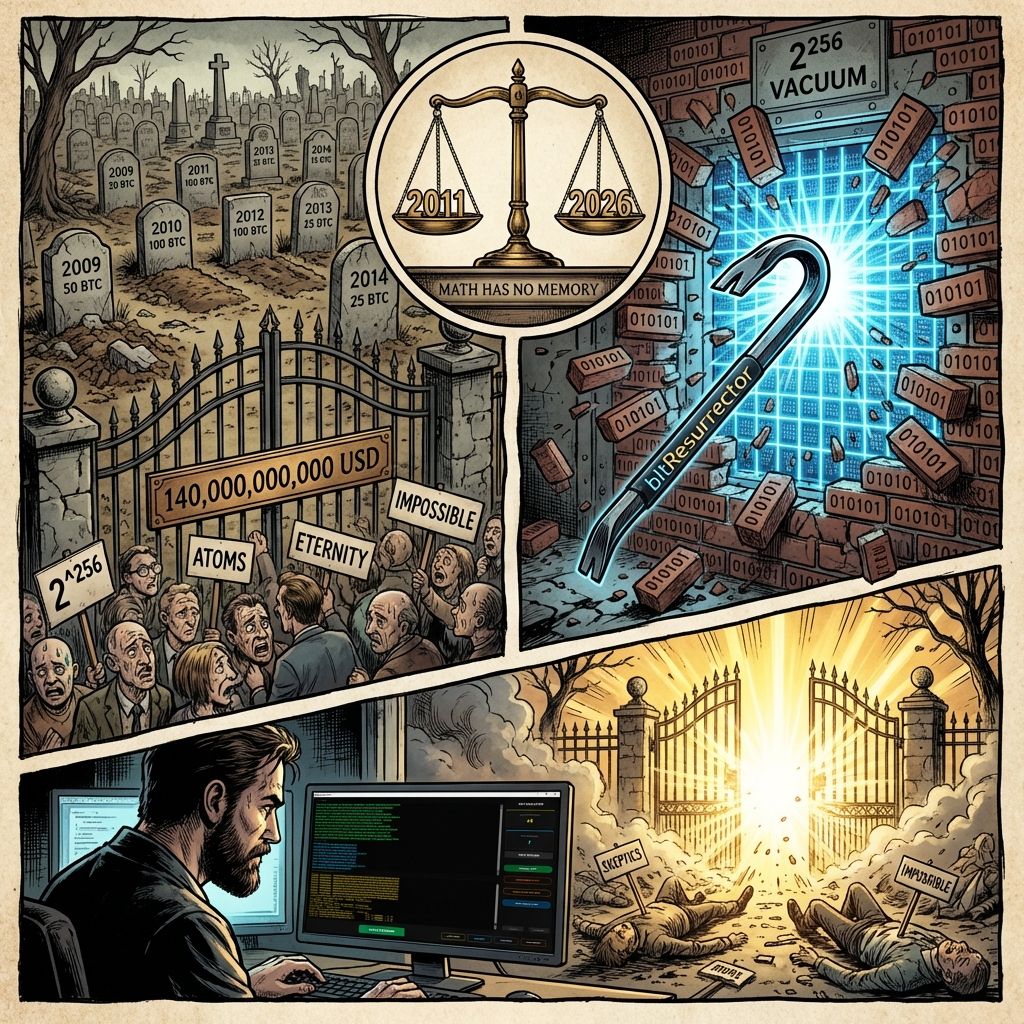
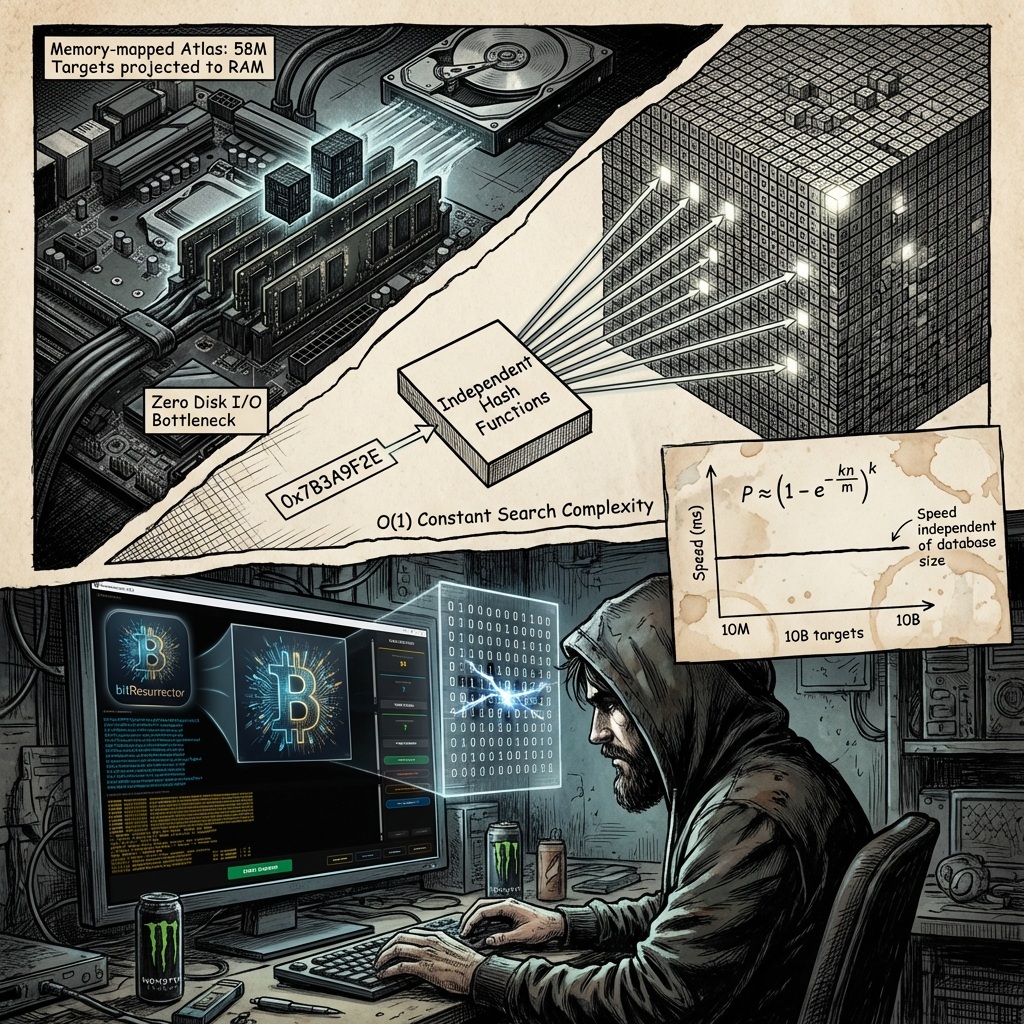
The system’s high efficiency is ensured by using a Bloom filter, which real-time matches generated addresses against a global database containing absolutely all addresses with a positive balance existing in the blockchain.
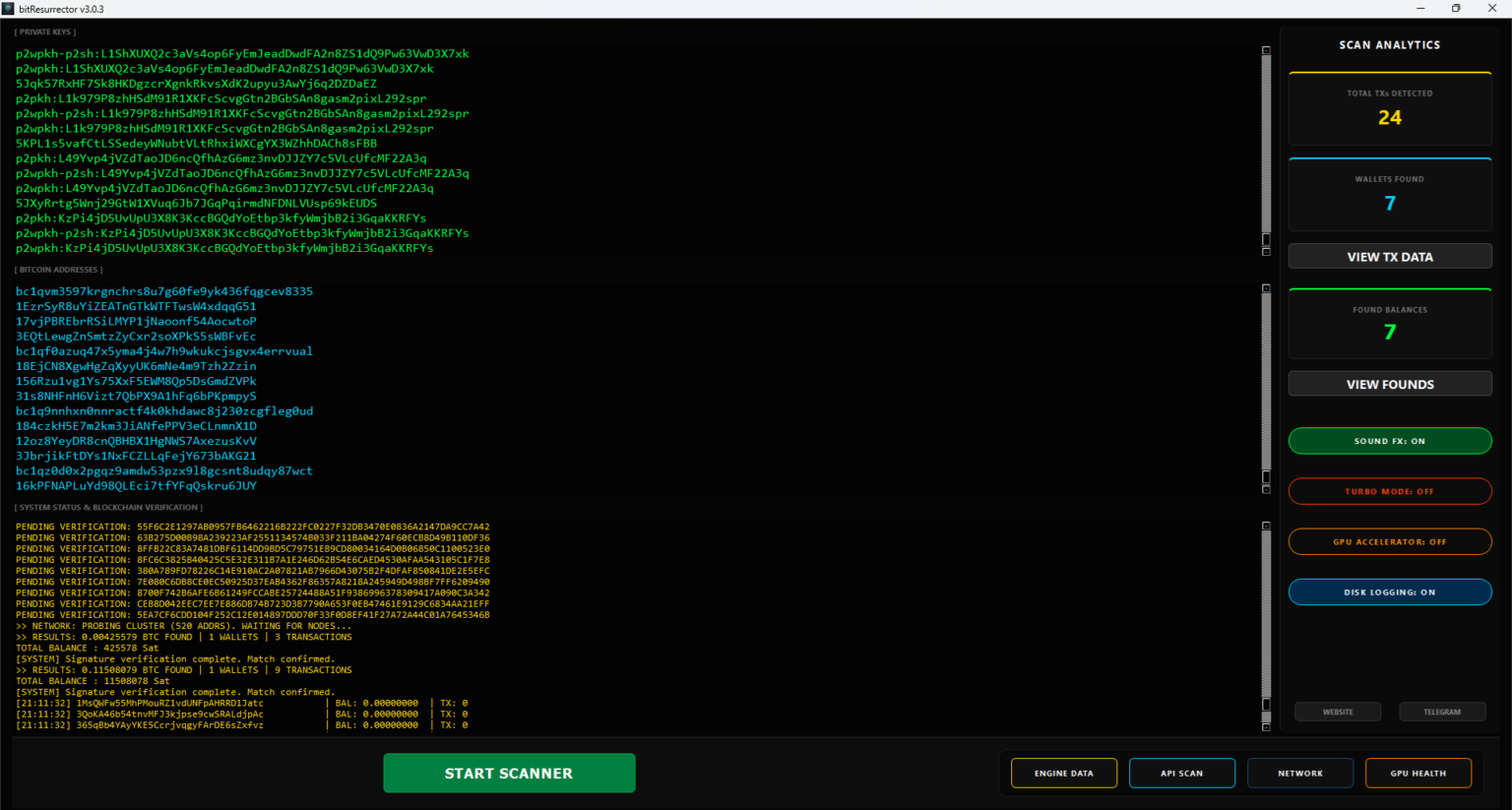
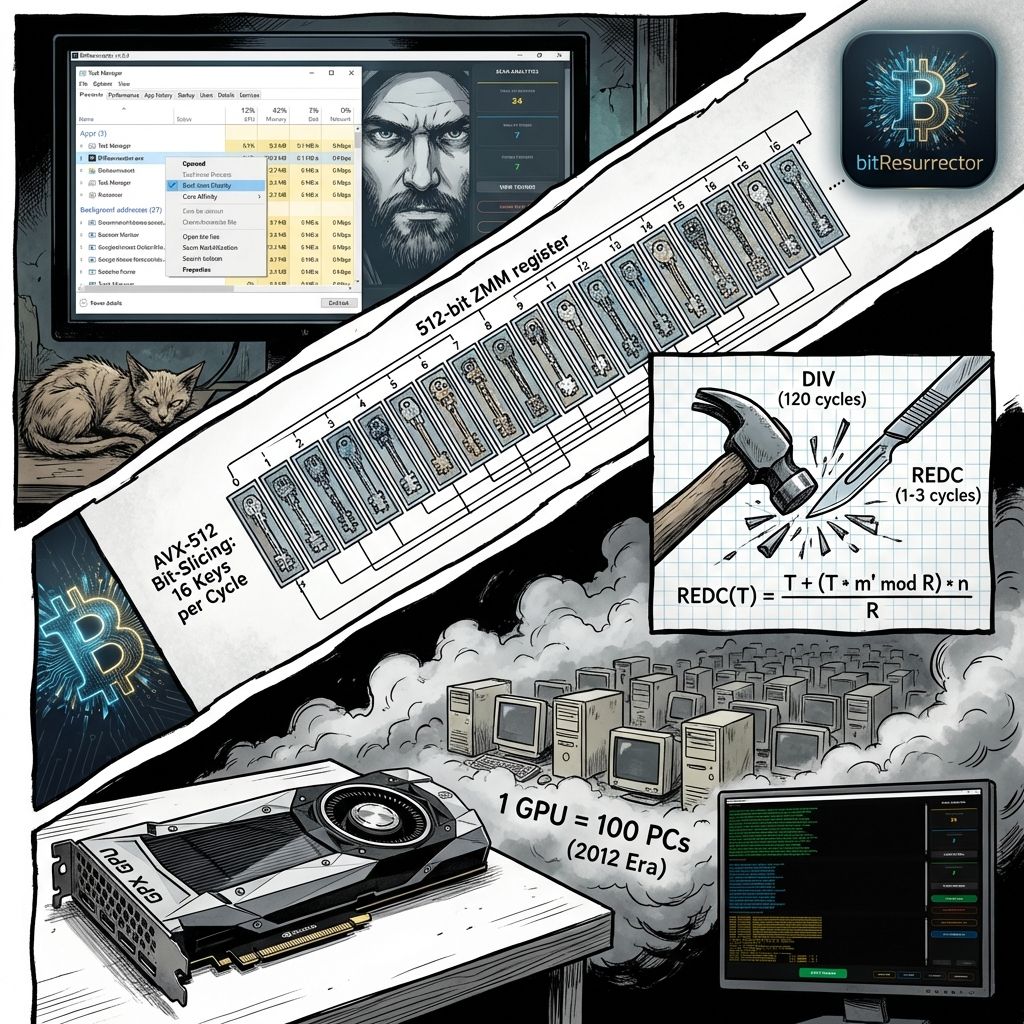
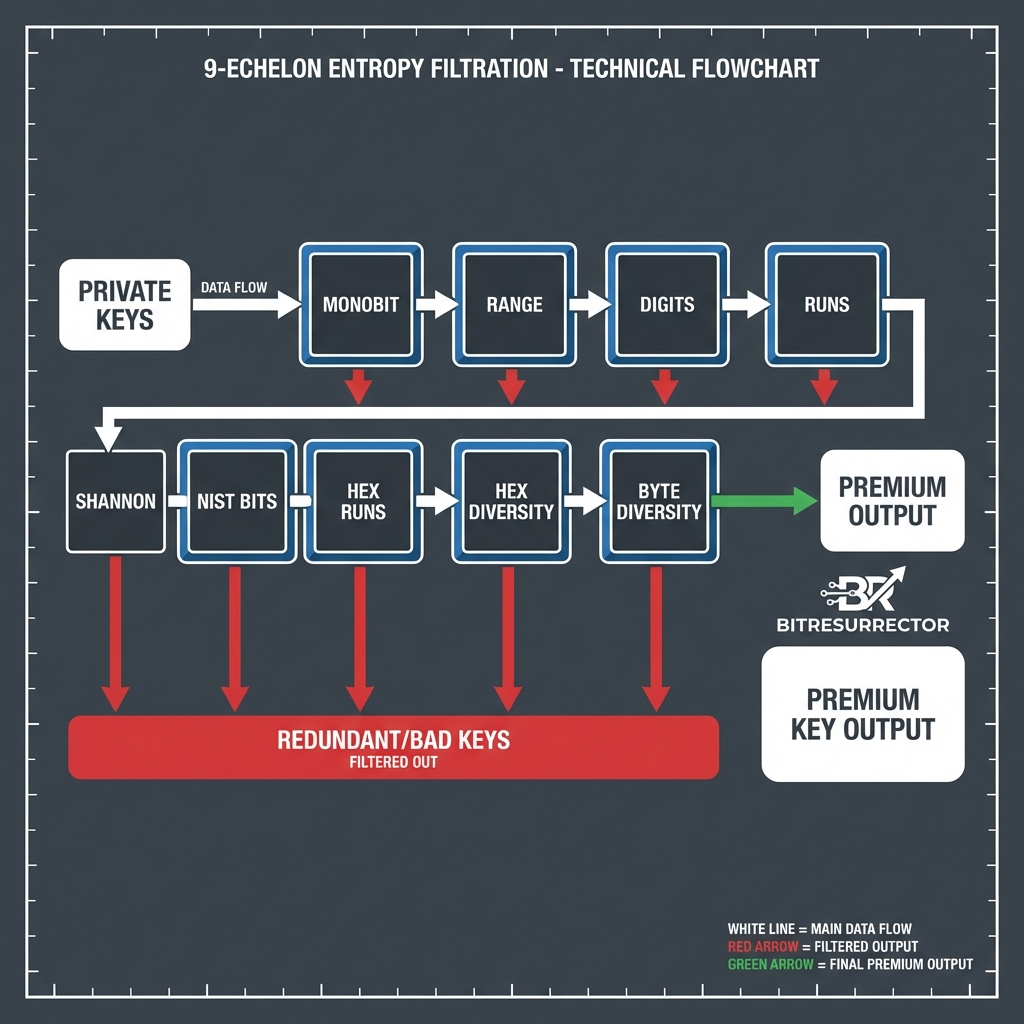
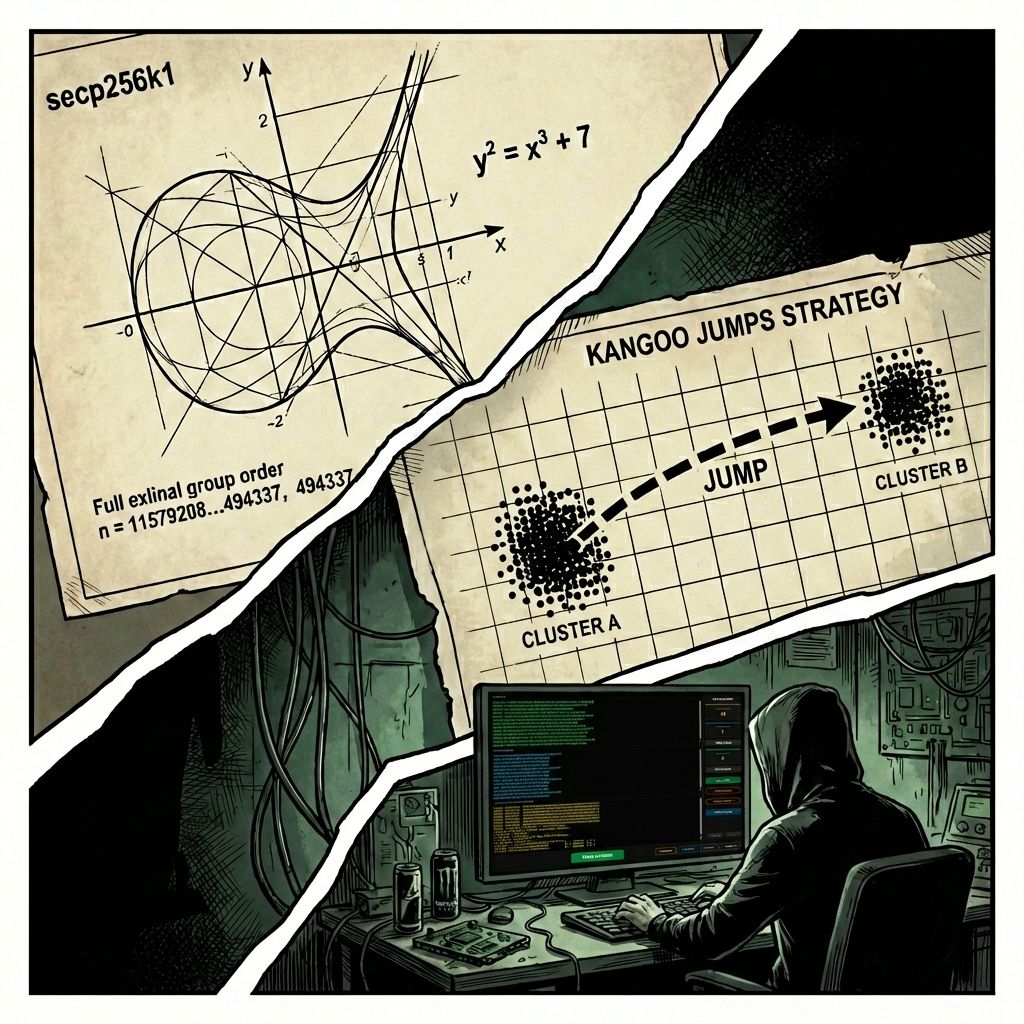
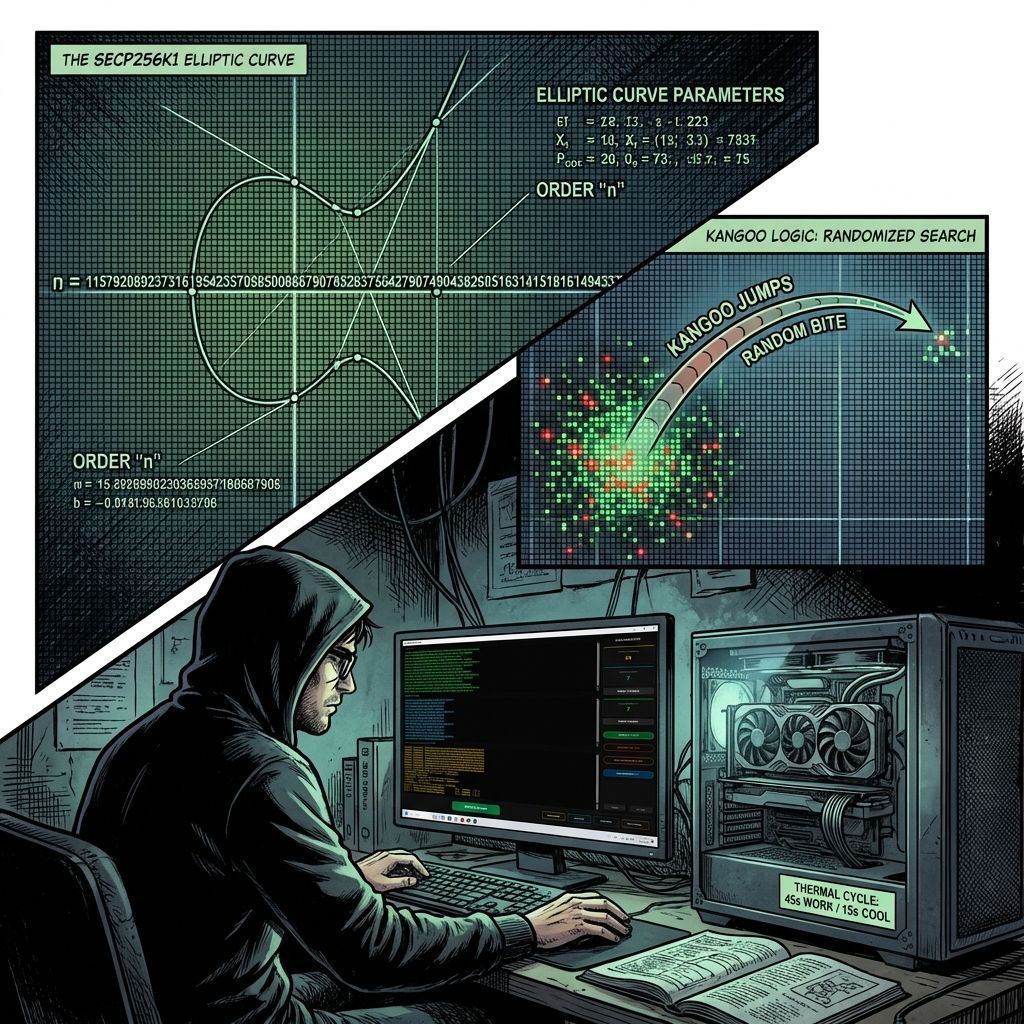
bitResurrector executes high-velocity private key reconstruction within the secp256k1 field, leveraging
Sniper Engine v3.37 and a local Bloom Filter Matrix for constant-time balance verification.